In today’s world of technology, certain terms gain prominence, and one such exciting phrase making waves is “Kpong Krnl Key.” This article covers the depths of kpong krnl key, exploring its features and shedding light on why it has become a focal point in the tech field.
Decoding Kpong Krnl Key: A Brief Overview
Before we plunge into the features, let’s decipher the essence of the Kpong Krnl Key. In simple terms, it’s a cutting-edge encryption key designed to bolster the security of digital communications. Its inception marked a paradigm shift in how we safeguard sensitive information online.
Features That Set Kpong Krnl Key Apart
1. Impenetrable Encryption
At the core of Kpong Krnl Key lies its unparalleled encryption capabilities. Employing state-of-the-art algorithms, it provides a virtually impenetrable shield against cyber threats, ensuring the confidentiality of data in transit.
2. Versatility Across Platforms
One standout feature is its adaptability across various platforms. Whether you’re safeguarding emails, securing financial transactions, or protecting sensitive documents, the Kpong Krnl Key seamlessly integrates, offering a universal solution to digital security concerns.
3. Dynamic Key Management
Unlike static keys, the Kpong Krnl Key operates on a dynamic key management system. This means that the encryption keys are constantly changing, adding an extra layer of complexity for potential attackers and enhancing overall security.
4. User-Friendly Interface
While the technology behind the Kpong Krnl Key is complex, its interface remains user-friendly. This makes it a viable option for individuals and businesses alike, fostering a culture of digital security without the need for extensive technical expertise.
5. Lightning-Fast Processing Speeds
In the realm of digital security, speed is crucial. Kpong Krnl Key doesn’t compromise on efficiency; it operates at lightning-fast speeds, ensuring that the encryption process doesn’t hinder the flow of data.
6. Scalability for Growing Needs
As businesses evolve, so do their security requirements. The Kpong Krnl Key is designed with scalability in mind, accommodating the growing needs of users without compromising its robust security features.
7. Integration with Existing Systems
A notable advantage is its seamless integration with existing security systems. This means minimal disruption during implementation, making it an attractive option for businesses looking to enhance their security infrastructure.
8. Continuous Updates for Evolving Threats
Digital threats are ever-evolving, and the Kpong Krnl Key recognizes this. Regular updates ensure that the encryption algorithms stay ahead of potential vulnerabilities, providing users with a proactive defense against emerging cyber risks.
9. Transparent Encryption Processes
Transparency is key in the digital age. The Kpong Krnl Key offers a transparent encryption process, allowing users to track and verify the security measures in place, instilling confidence in the efficacy of the system.
10. Cost-Effective Security Solution
In a landscape where cybersecurity solutions can be financially daunting, the Kpong Krnl Key stands out as a cost-effective option. Its robust features come without an exorbitant price tag, making high-level digital security accessible to a broader audience.
Let us understand more important and informative topics on webplore.com
GetKpong Krnl Key
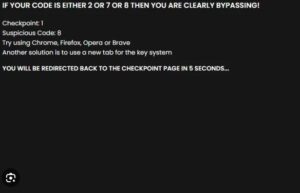
The krnl key serves as a distinctive code that provides authorization for accessing particular content or resources. In case the link provided above is not functional, you can manually copy the given URL and paste it into a new tab to reach the information you’re seeking.
https://cdn.krnl.place/getkey.php
or
https://cdn.krnl.place/getkey
Conclusion: Embracing a Secure Future with Kpong Krnl Key
In conclusion, the Kpong Krnl Key emerges not just as a security solution but as a paradigm shift in the way we perceive digital protection. Its versatile features, user-friendly interface, and cost-effectiveness position it as a frontrunner in the realm of cybersecurity. As we navigate the complexities of the digital landscape, embracing innovations like the Kpong Krnl Key becomes imperative for a secure and resilient future.